To celebrate Star Wars Day, I thought I would share a few ways in which the Empire did not adhere to information security best practices, and that enabled the Rebels to win.
To be clear: I do not support the Empire, the Sith Lords, or any other types of scum and villainy. Nor am I trying to portray the Rebel Alliance as a weird, Force-wielding, Galactic hacker consortium or something. But had the Empire not been so lax in their security controls, Emperor Palpatine and his buddies might have been able to bring their “order and peace” to the galaxy.
Social Engineering
Social Engineering: Social engineering is an attack that uses human interactions and plays on human weaknesses to break established security procedures.
Scene: Luke and Han, dressed as Stormtroopers, escorting Chewbacca to the prison block (Star Wars IV: A New Hope).

Lots of things going on here. First, no one wants to mess with a Wookie. Others were less likely to get involved when they saw that the Wookie was being escorted by two (only two) Stormtroopers. Luke and Han knew that if they looked like they knew what they were doing, they could walk around in plain sight without being questioned by anyone. Even after arriving at the detention block, the supervising guard did not suspect them as being bad guys, and only questioned them on a matter of paperwork. Sure, everything fell apart at that point — one of the security controls finally kicked in. But Luke, Han, and Chewie were able to walk pretty much anywhere they wanted on the Death Star by exploiting social engineering flaws.
Lesson: People — not just the bad guys — exploit social engineering gaps every day. When was the last time you piggybacked someone into a controlled building? The really bad guys know this as well, using our politeness (holding a door open for someone) against us. It is extremely hard to break those habits, which is why your security guys are constantly reminding you about them. Who knows if the guy you are holding the door for is coming to blow up the building (or the Death Star)?
Identity and Access Management
Identity and Access Management: Identity and access management is the system used by entities to allow and prohibit access to resources controlled by the entity.
Scene: Luke, Leia, Han, C3PO, and Chewie on the Shuttle trying to land on Endor (Star Wars VI: Return of the Jedi)

The Rebels have stolen (property theft, probably due to lack of physical security controls on the part of the Empire) a small Imperial shuttle and are landing a team on Endor to blow up the shield generator protecting the second Death Star. Apart from using the Imperial shuttle, the Rebels have also stolen a security code that will allow the shuttle to land on the forest moon. There are multiple points that the code could have been rejected, with the admiral even claiming that it was an older code. Eventually, the Rebels are given clearance and allowed to land.
Lesson: Identity and access management is a difficult topic for most businesses. Larger businesses MUST have a solution for IAM in place because their employees turn around much more frequently than in smaller companies. Unfortunately, there are always gaps — the employee who was terminated months ago still has an active security badge, because the two systems are not connected and the administrator of the badge system was not notified (or on vacation or whatever) that the employee was no longer with the company. All businesses need to have controls in place and audit them regularly to make certain that there are as few gaps as possible.
Data Security
Data Security: Data security includes the methods used by an entity to protect all manners of data from those not authorized to use it.
Scene: Princess Leia and her crew intercept the technical plans to the Death Star (Star Wars IV: A New Hope)
The very first scene in the very first movie (yes, the original Star Wars will ALWAYS be the first movie to me) starts with an epic space battle — the Empire is beating up a Rebel blockade runner that happens to be carrying Princess Leia and the technical plans for the first Death Star. 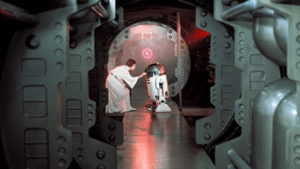 The Rebels had intercepted those plans, and the Princess was in the process of delivering them back to her home world when she was captured. The Rebels had been a thorn in the side of the Empire up to that point, but now they had the data necessary to severely cripple the Emperor’s goal of galactic domination using the Death Star.
The Rebels had intercepted those plans, and the Princess was in the process of delivering them back to her home world when she was captured. The Rebels had been a thorn in the side of the Empire up to that point, but now they had the data necessary to severely cripple the Emperor’s goal of galactic domination using the Death Star.
Lesson: The Empire should have done a better job securing the plans. In Rogue One: A Star Wars Story, we find out that the data was stored in the Imperial library on Scarif. We don’t know if the data drive that Jyn Erso stole was encrypted or not (another tenet of data security), but even if it was encrypted at rest, it was transmitted using an unsecured methodology, allowing the Rebel Alliance to intercept them (and break the encryption, if necessary). Most companies and entities have intellectual property/trade secrets/military secrets that they don’t want others to have. Not only should that data be encrypted and protected, but the networks and devices that send and store the data need to be protected as well.
In conclusion, I know that some of these examples are a bit convoluted, and I am sure there are some out there that would like to debate the finer details of exactly what happened in the movie (contact me — we can talk specifics (I had to amend some things for brevity’s sake)). But the point is that Star Wars Day is just another opportunity to remind you about the importance information security has on so many aspects of our lives. If Star Wars makes that point a little more enjoyable, then I’ve accomplished that goal!
Enjoy the day, and “May the Fourth” be with you!
______________________
A distributable version of this blog to share with your friends and colleagues can be found here:
https://info.enterprisemanagement.com/star-wars-day-security-awareness-research




