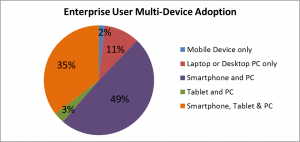
Have you ever tried to create a major slide presentation on a tablet? Or edit a large spreadsheet? Or write a long document? Probably not. While it’s certainly possible to perform more substantial business tasks on a tablet, the small screen real estate and limited system resources (e.g., processing speed, memory, graphic support, etc.) are typically insufficient in current tablet form factors. However, carrying a laptop around with you everywhere you go just so you can access email is not very practical either. The reality is that we live in a multi-device world where the average worker employs 3 – 5 different computing devices in the regular performance of their job function. . . . and I would argue that’s exactly how it should be. Each user employs the device they prefer to optimally perform tasks at any particular time or place.
Top 5 Trends in 2015 for Unifying PC and Mobile Management
By Steve Brasen on Feb 12, 2015 9:18:00 PM
Gaining Data Control with BYOD and Bluebox
By David Monahan on Apr 22, 2014 10:51:06 AM
What’s the issue with BYOD? Data Control… What’s the issue with Data Sharing? Data Control!
Don’t Believe Everything You Read – Especially About Enterprise Mobility!
By Steve Brasen on Jan 17, 2014 11:12:53 AM
I just got off the phone with a reporter from a major industry trade magazine (no names please!) who is preparing an article on enterprise mobile device adoption. Wanting to help ensure accuracy in the reporting, I provided him with statistical details from our recent research into the use of mobile devices in the enterprise and stepped him through the findings. He was fascinated by the results and asked lots of follow-up questions. In the end, however, he admitted he would likely not be able to use any of the information in his article (say what?!). Apparently, his editor had specifically tasked him with writing an article showcasing how tablets are rapidly replacing PCs in the workplace, even though this is completely contradictory to reality.
ForeScout Technologies has a Knack for NAC (and more) with ControlFabric and CounterACT
By David Monahan on Jan 16, 2014 8:35:02 PM
Recently I briefed with ForeScout Technologies, a Network Admission/Access Control (NAC) vendor, to get an update on the CounterACT platform it has been delivering and developing for a few years and to see its recently announced ControlFabric technology. I thought it wise to take another look at NAC vendors and how they address BYOD, rogue, or non-compliant devices that can be the source of many compliance and security headaches including advanced/targeted threats.
Maybe We Should Call It The “Pre-Post-PC” Era?
By Steve Brasen on Jun 6, 2013 9:48:41 AM
IT marketing hype has generated quite a few ridiculous and sometimes outright bizarre phrases to describe trends in technology adoption, but few on the list of the absurd top the insistence that we live in a “post-PC” era. The concept of “post-PC” derives from the (correct) fact that mobile device adoption has broadly accelerated, but makes the incorrect assumption that this is causing a substantial decrease in PC use. Nothing could be further from the truth – especially in relation to the business use of desktop and laptop PCs.