The Evolution of the “Endpoint”
Over the past few years, the perception of what an “endpoint” is, and therefore the definition, has changed. The original perception was a user workstation independent of operating system. With the expansion of functionality, data persistence, Internet connectivity, and ultimately the threats against them, that definition no longer applies. Laptops became included, then smartphones, servers, tablets, internal file shares, and dedicated or special function devices such as point of sale terminals and processors.
The Truth Behind the Scope of the Endpoint Problem in the Enterprise
By David Monahan on Jan 12, 2017 6:41:06 PM
A Tribute to IoT Device Security Researchers
By David Monahan on Jan 3, 2017 9:34:22 AM
This blog in the Internet of Things (IoT) series comes as a tribute to security researchers everywhere. The autumn’s largest security-focused show is the Black Hat Security conference. If you are not familiar with Black Hat, it is a tech conference that started in 1997 and covers numerous security topics in various presentations that are fairly to highly technical. As mentioned in the first blog in the series, IoT-like systems have been around a long time. However, researchers began paying more public attention to IoT around 2011. Visibility on the subject of the security, or lack thereof, of IoTincreased in 2011, when researcher Jay Radcliffe demonstrated that medical devices; in this case, his own automated insulin pump, could be hacked to deliver a lethal dose of insulin.1 Since that time, there were numerous other IoT hacks in various fields, including:
IoT Enterprise Risk Report
By David Monahan on Dec 21, 2016 2:47:12 PM
ForeScout recently released an IoT Enterprise Risk Report based on research from ethical hacker Samy Kamkar. Based on Kamkar’s findings, the report on IoT security issues could readily be renamed something like, “IoT: the bane of the enterprise environment,” or “IoT brings new meaning to the term ‘Enterprise Risk’.”
The Top 5 IoT Lessons I Learned From Hollywood
By David Monahan on Sep 23, 2016 12:07:46 PM
In my last IoT blog, I talked about the history of IoT and the evolution of issues surrounding IoT devices. In this part of the series, we will expand on the issues around IoT and the data it collects.
Effective Security Requires a Change in Mindset and the Protection Paradigm
By David Monahan on Aug 24, 2016 11:05:53 AM
Nearly every day another successful breach is reported. In 2016 alone, organizations from major governmental agencies such as the IRS and Department of Defense, to major retailers including Wendy’s, have succumbed to attack. These organizations are not alone; every major business and governmental sector has been compromised. Large tech companies such as LinkedIn and Oracle, healthcare providers including Premier Healthcare (as well as numerous hospitals), manufacturers, major educational institutions, and large financial organizations have all succumbed to either internal or external threats.
IoT Devices in the Network: Can you find them?
By David Monahan on Aug 10, 2016 2:26:18 PM
In the last year or so, the topic of Internet of Things (IoT) received a lot of attention. Both the concept of the topic and scope of what should be included in IoT changed dramatically in that time. The first commercialization of IoT were wearables such as GoogleGlass. Shortly thereafter came the next wave, with devices such as smart watches. The first security concerns were focused on personal safety due to user distractions, similar to those voiced when smartphones became popular, and then came the invasion of privacy concerns. However, shortly after the first hackers got hold of them and identified attacks to gather data from them. At that point, the view on IoT expanded to recognize that the concept of IoT was actually much broader and had more significant impacts than privacy.
The Desperate Need for Accuracy and Efficiency in Security for Detecting Network Intruders and Other Threat Actors Quickly
By David Monahan on Apr 14, 2016 2:37:49 PM
According to 2015 research reports published by Ponemon, Mandiant, and others, median intruder dwell time in a target network prior to detection ranges from just under to just over 200 days. That is a little over six months and as everyone agrees, totally unacceptable.
HEAT Software Meets the Need for Endpoint Protection Head-On
By David Monahan on Dec 11, 2015 12:40:49 PM
In many organizations, endpoints see virtually constant change. Users access, download, and utilize applications, data, drivers, files, toolbars, widgets, etc., introducing both new security threats and undocumented changes in systems and processes. For better or for worse, all of these activities leave their mark on the endpoint.
The Rise of Thingbots in the Internet of Things (IoT)
By David Monahan on Nov 20, 2015 12:50:39 PM
The Internet can be a pretty scary place. Places like the dark web exist in the form of trading houses with stolen personal information from credit cards and social security numbers, to health records and full identities being obtained for a price. Malware development and deployment and other attack services such as DDoS and botnets can be rented by the hour. Recent reports indicate that DDoS attacks are increasing in both frequency and size, and the problem of botnets being used as attack networks or launch points in DDoS and other malicious activities is significant. Indications are that it will only continue to get worse.
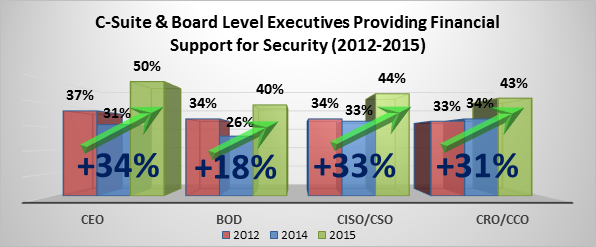
EMA Research Shows that Cyber Security is Achieving Executive Visibility in a Big Way
By David Monahan on Nov 20, 2015 12:50:32 PM
One of the services that EMA provides to the tech industry is research. During the course of the year, numerous projects are launched to help IT consumers and vendors understand market perceptions. EMA then provides analysis and forecasts on trends based upon those perceptions.